
# Core Value of IaC and Terraform
In cloud-native and DevOps practices, Infrastructure as Code (IaC) has become the golden standard for modern IT operations. Traditional manual management of servers, networks, and storage is not only inefficient but also prone to environment drift, making it difficult to ensure consistency across testing, staging, and production environments.
Terraform is an IaC tool released by HashiCorp that uses declarative HCL syntax, enabling operations and development teams to manage infrastructure just like application code. Its core advantages include:
- Environment Consistency: Infrastructure is defined as code, ensuring completely consistent deployments every time.
- Version Control: Infrastructure changes are traceable and support GitOps processes.
- Multi-Cloud Support: Unified management of resources across multiple platforms like AWS, Azure, Kubernetes through the Provider mechanism.
- Automated Orchestration: Combined with CI/CD tools (like Zadig), achieve automated infrastructure changes and management.
However, relying purely on Terraform CLI to execute terraform plan and terraform apply still requires manual operations and carries risks of human error. Deep integration of Terraform with Zadig to implement automated change processes has become the best practice for enterprise-grade DevOps, effectively improving both safety and efficiency of changes.
# Enhancing Terraform Workflows with Zadig
Zadig, as a cloud-native DevOps platform, can deeply integrate with Terraform to build secure, efficient, and standardized infrastructure automation processes, achieving:
✅ Manual Approval Process —— Prevent misoperations and enhance change safety ✅ Sensitive Information Security Control —— Prevent hardcoded secrets and leakage risks ✅ Automatic Trigger Execution —— Support GitOps mode, code changes trigger infrastructure deployment
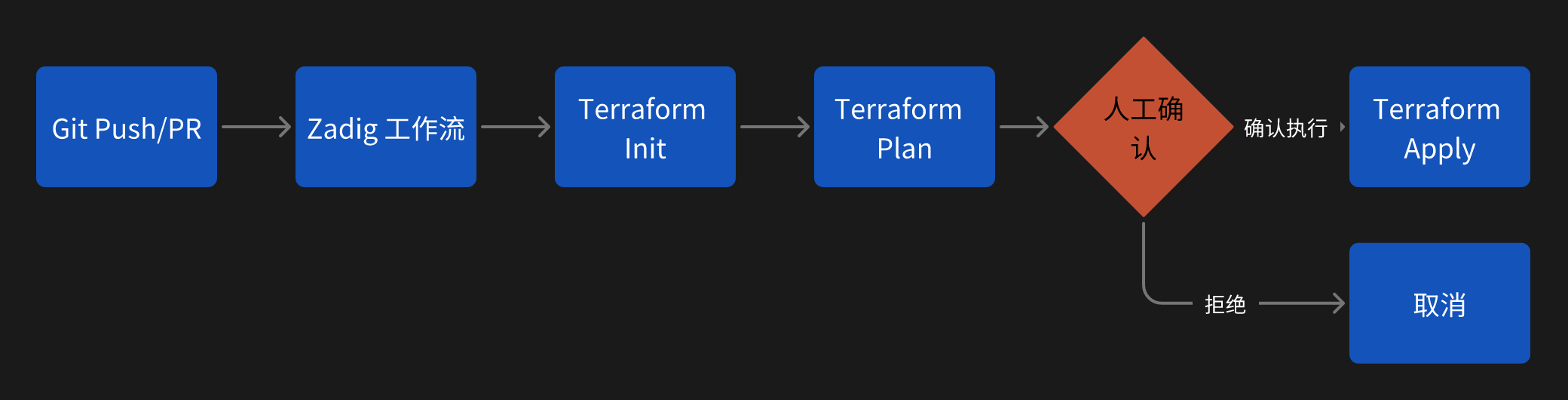
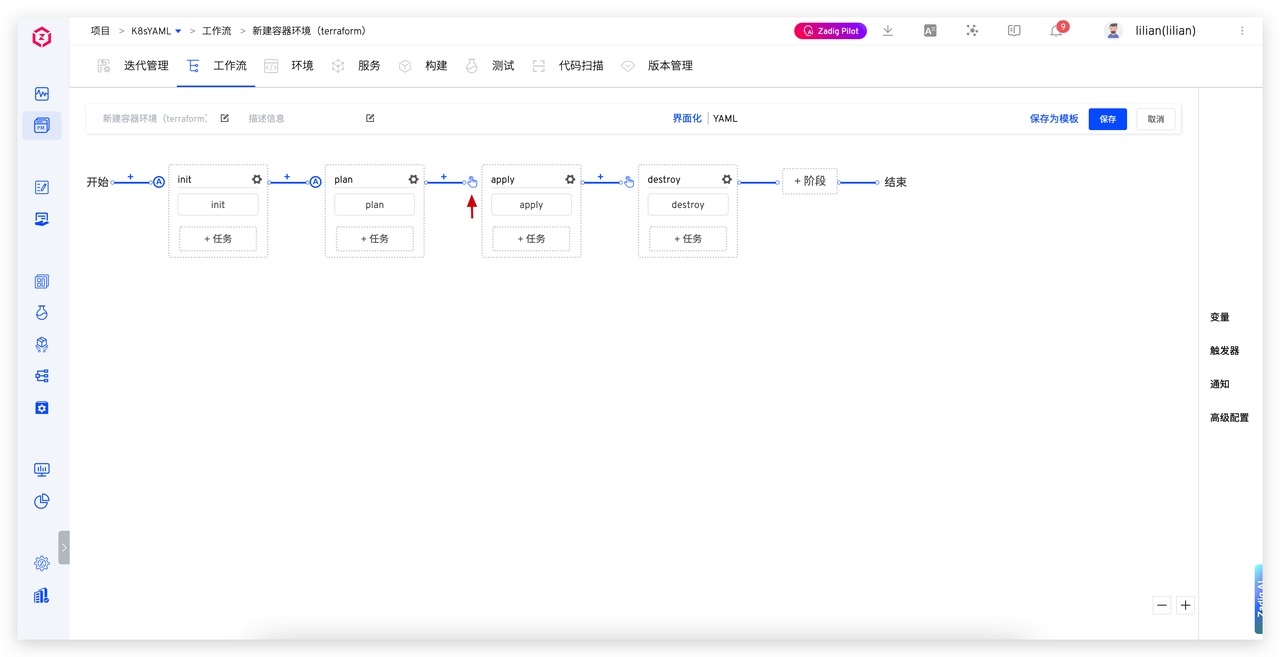
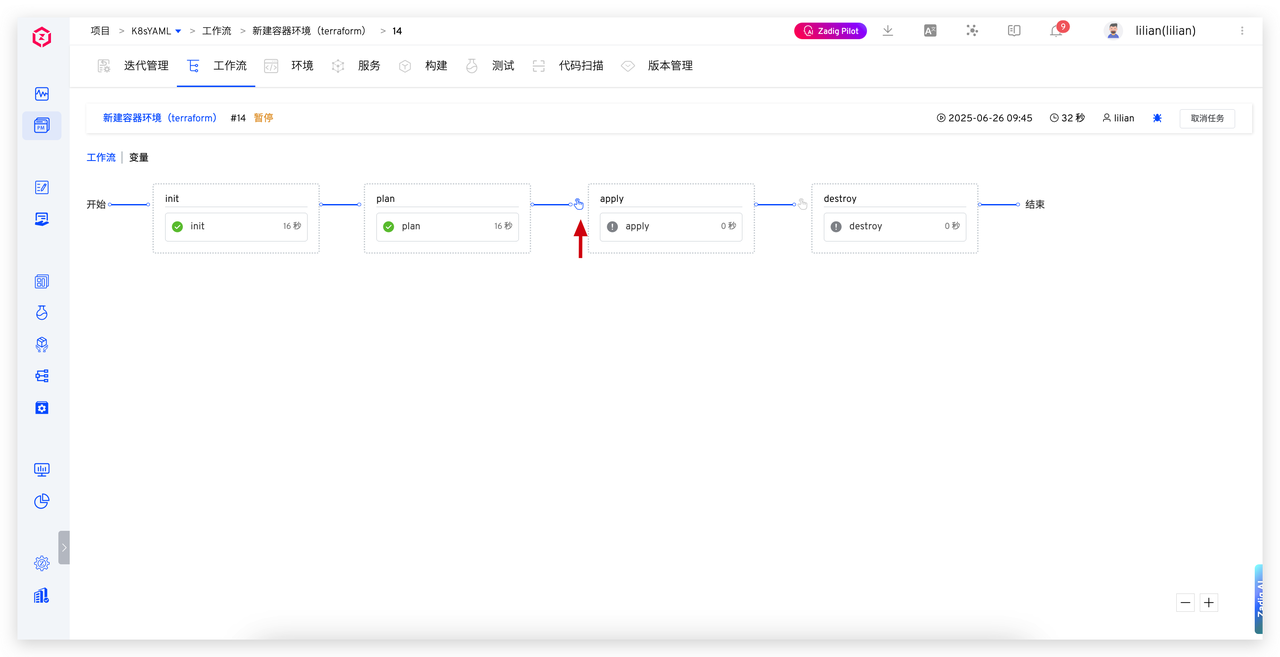
Typical automation process:
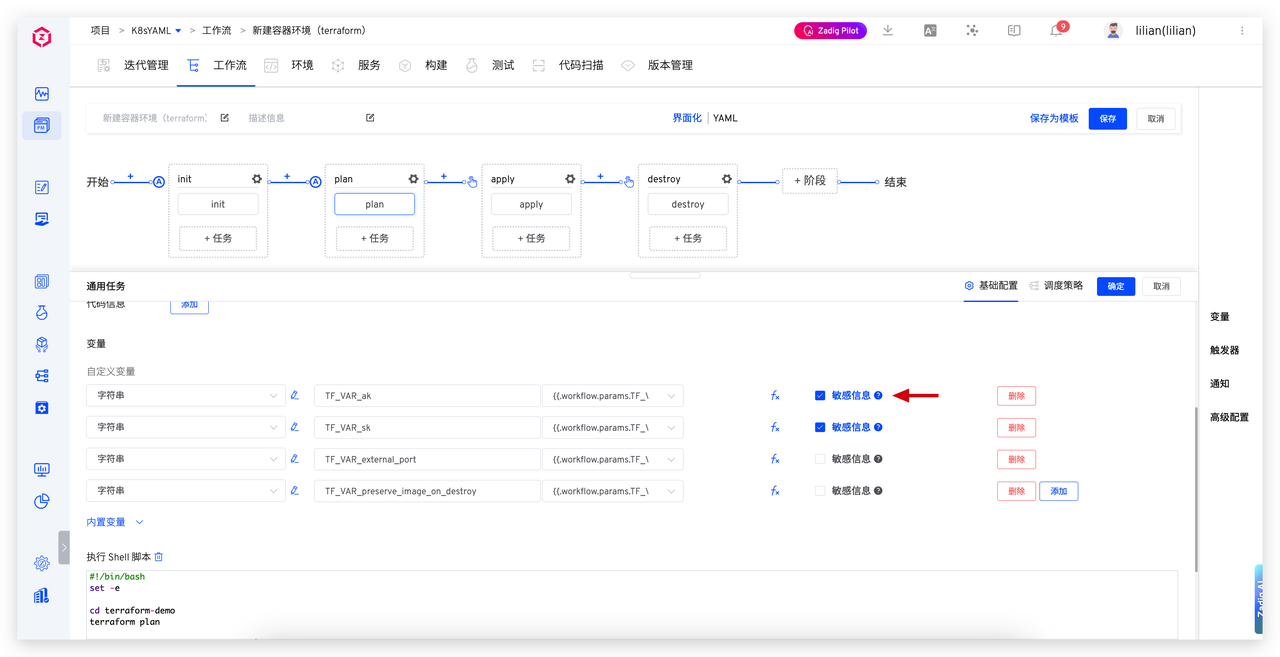
# Basic Configuration Process for Workflow Tasks
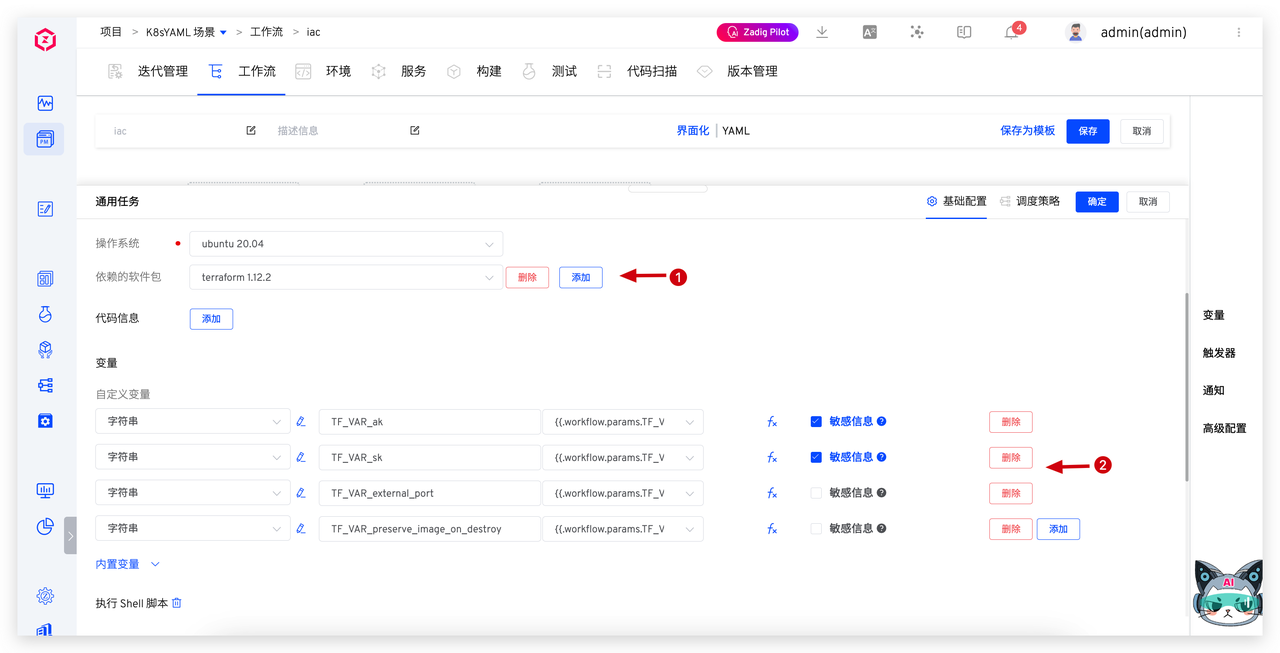
Create a workflow in Zadig and add three "General Tasks" corresponding to the three key stages of Terraform:
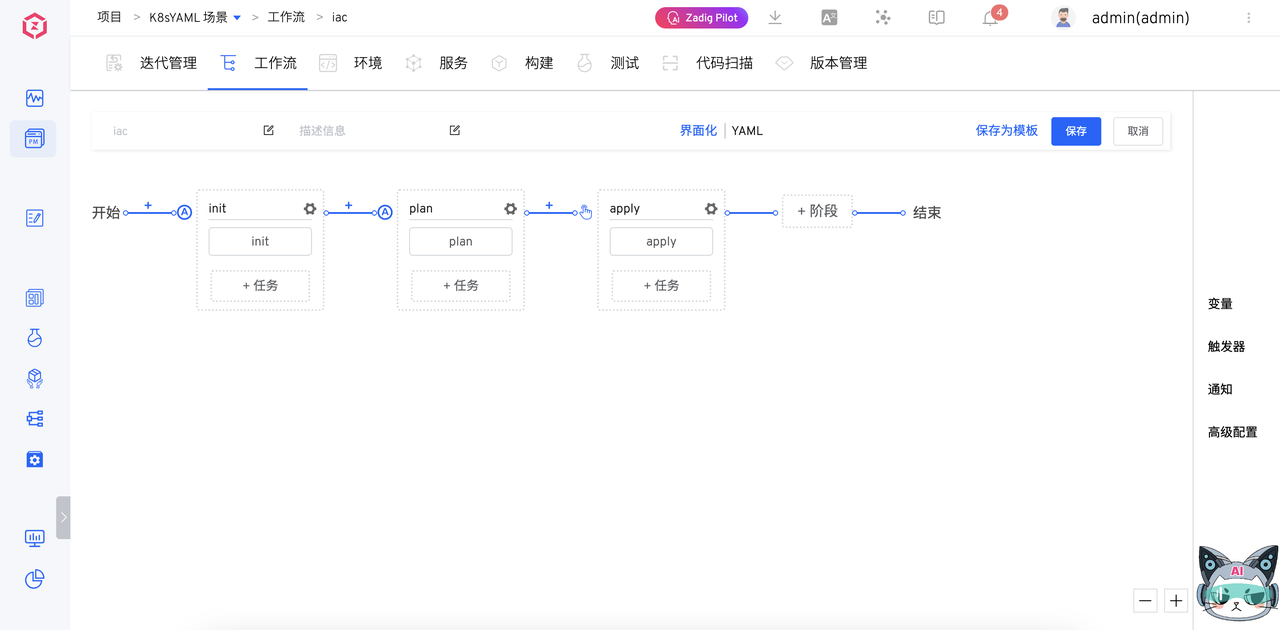
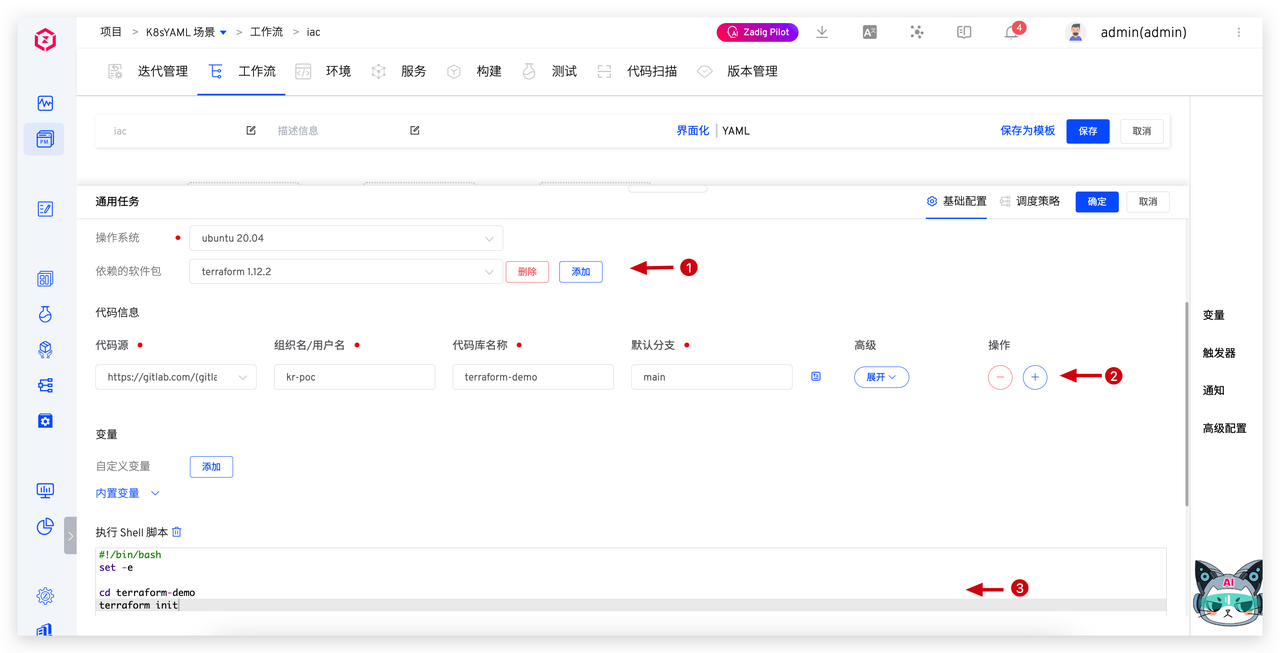
- Init Stage: Project Initialization
Execute terraform init command to pull code and initialize execution environment.
- Add Terraform software package dependencies
- Configure code repository path
- Write initialization script commands
Configuration as follows:
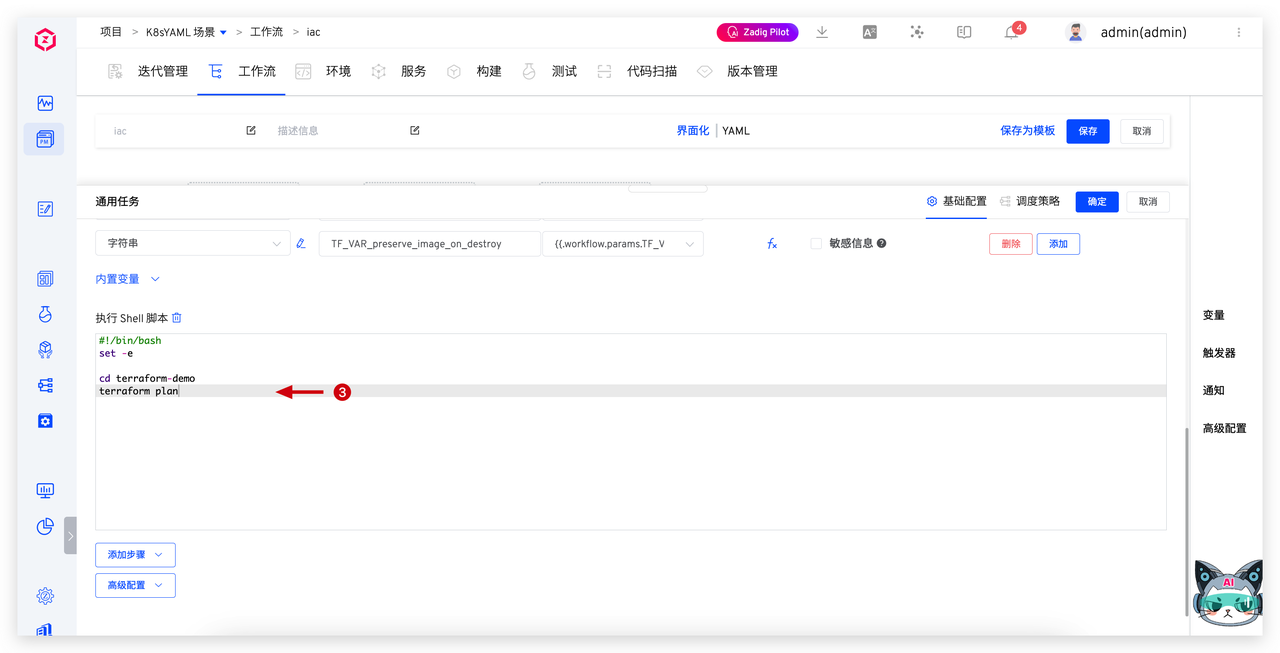
- Plan Stage: Generate Change Plan
Execute terraform plan to preview changes about to be executed, ensuring operations are transparent and controllable. Configuration as follows:
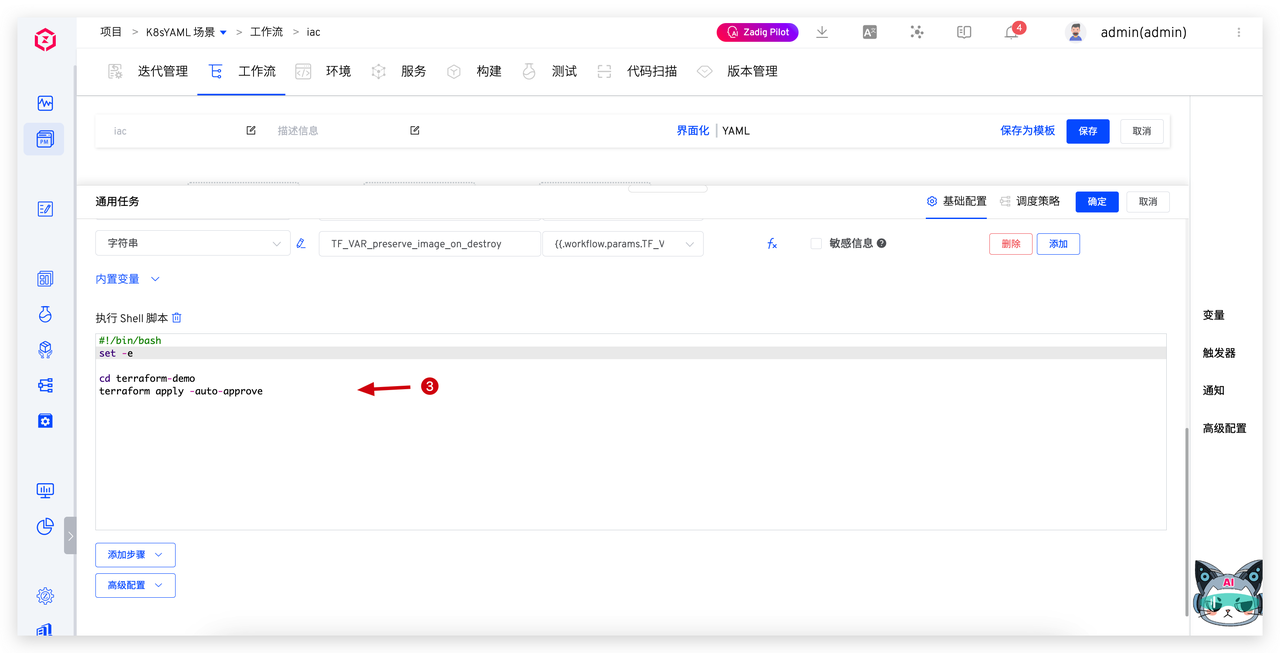
- Apply Stage: Execute Infrastructure Changes
Execute terraform apply to formally apply changes and complete infrastructure deployment or adjustments. Configuration as follows:
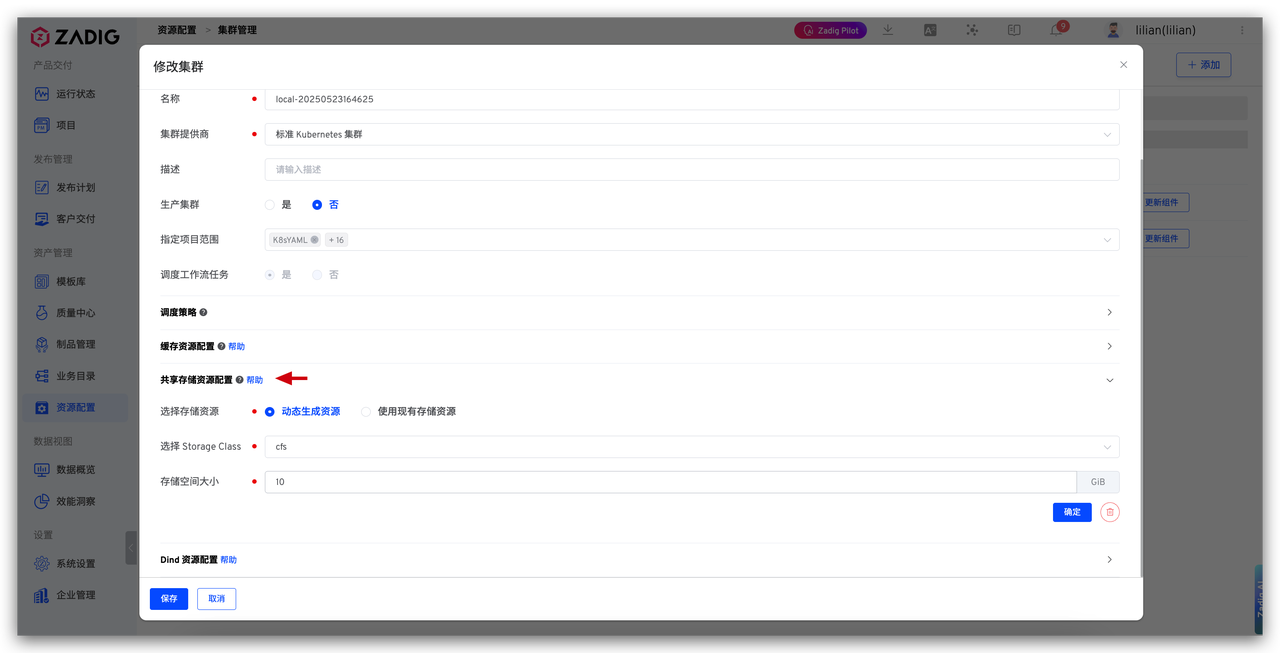
- Shared Storage Configuration: Maintain State Consistency Between Tasks
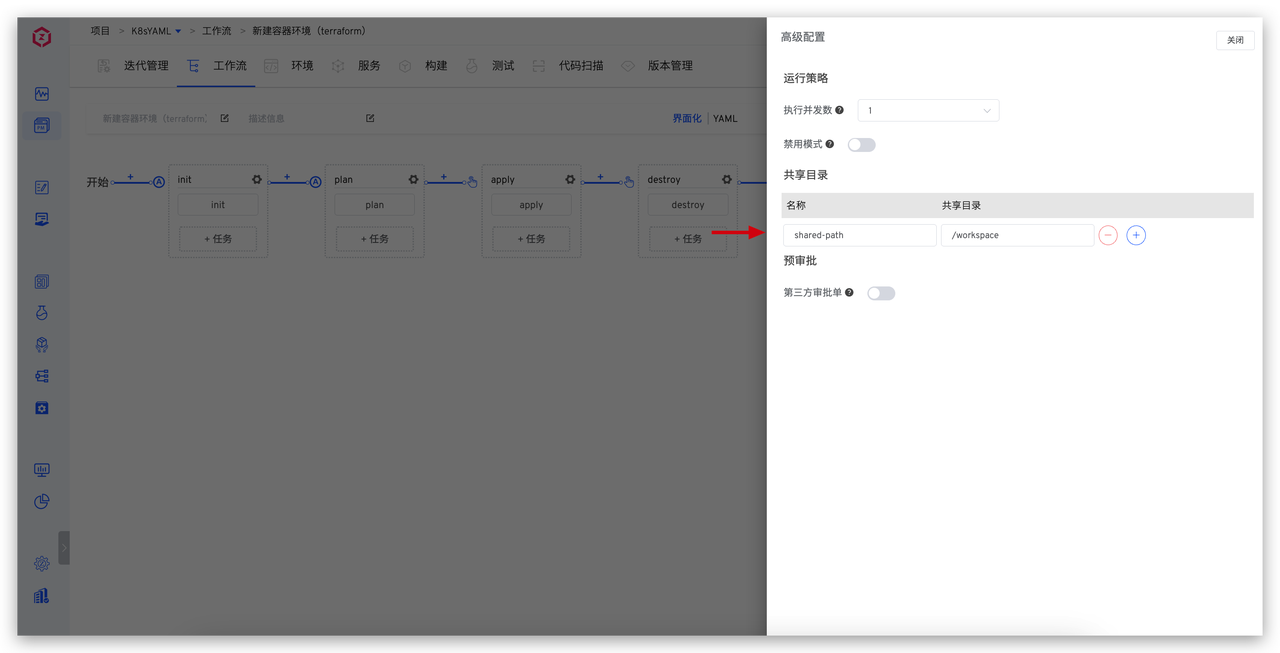
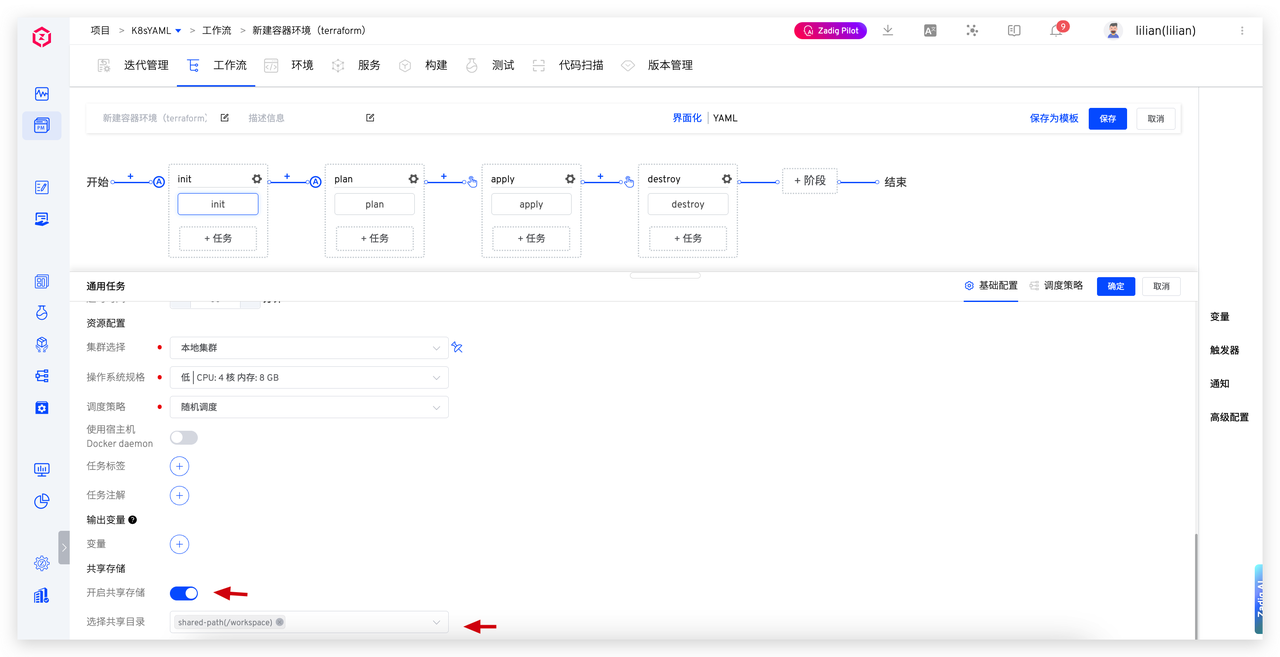
To share working directories and execution contexts between multiple tasks, Zadig supports "Shared Storage Resource Configuration":
- Add shared storage resources in cluster management
- Bind shared directories in workflow advanced settings
- Enable and select the same shared storage in Init, Plan, Apply tasks
This ensures Terraform state files and execution contexts are smoothly passed between stages, avoiding environment inconsistencies.
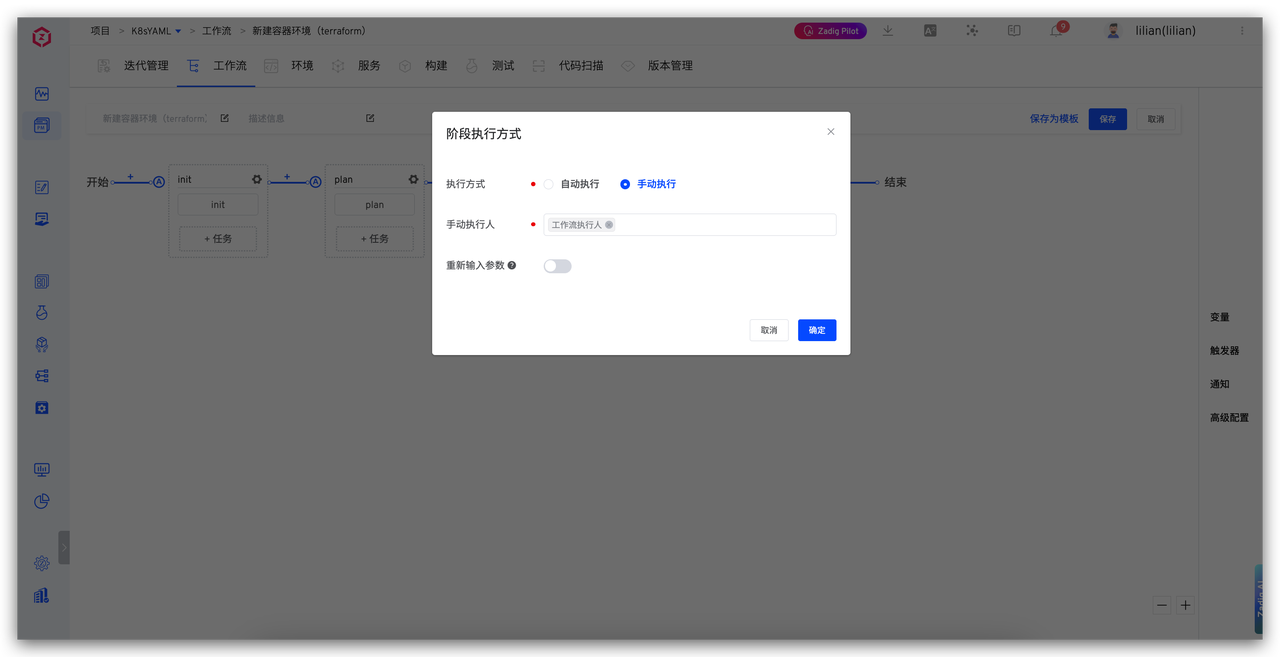
# Manual Confirmation Mechanism: Ensure Change Plans Meet Expectations
To enhance process controllability, manual confirmation steps can be added before executing terraform apply. Zadig provides built-in manual execution nodes, allowing operations personnel to review plan output before deciding whether to continue execution.
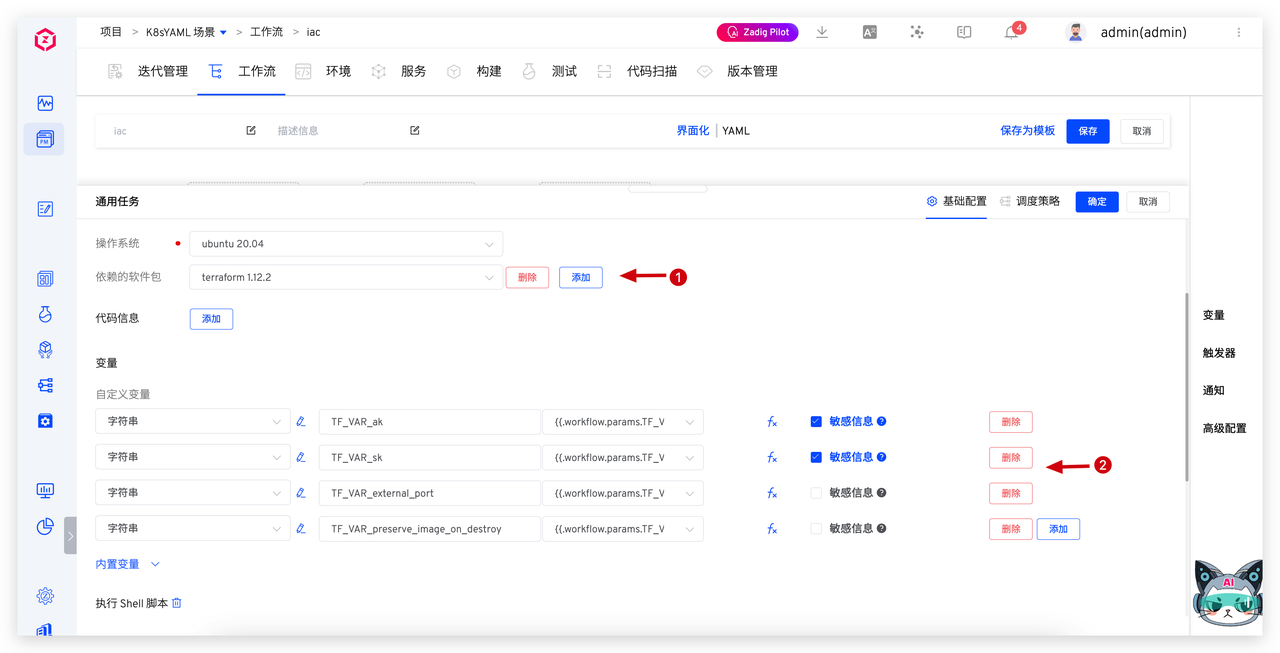
# Sensitive Information Management: Safeguard Credential Security
Terraform often involves sensitive information such as cloud service AK/SK keys and database passwords. Traditional approaches often hardcode or expose these in environment variables, creating serious security risks.
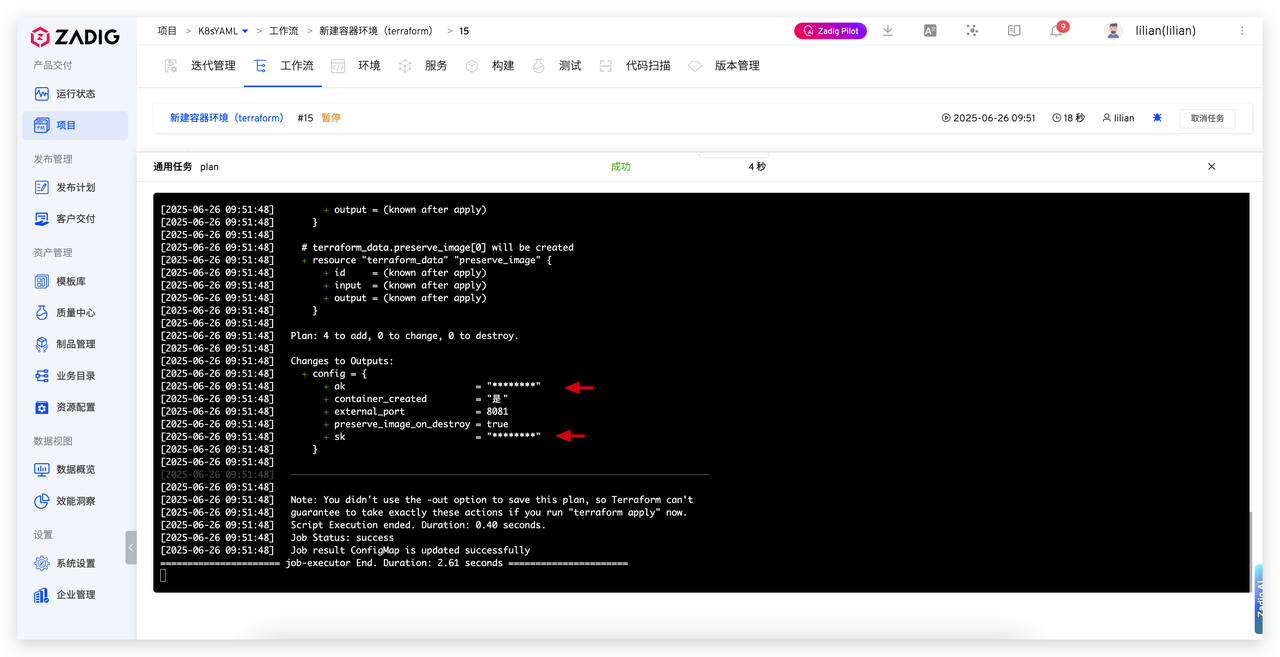
In Zadig, the "Sensitive Information" feature can centrally manage keys, automatically injecting and masking them during task execution, ensuring:
- Credentials are not written to logs or interfaces
- The entire process complies with enterprise security compliance requirements
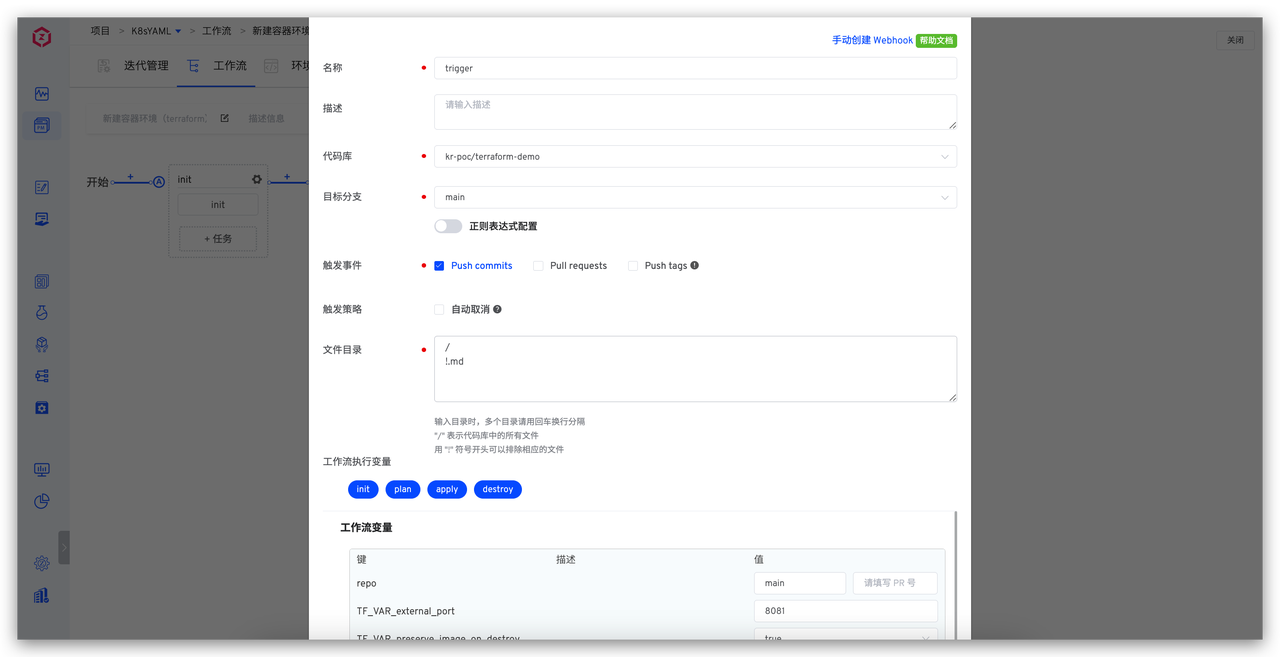
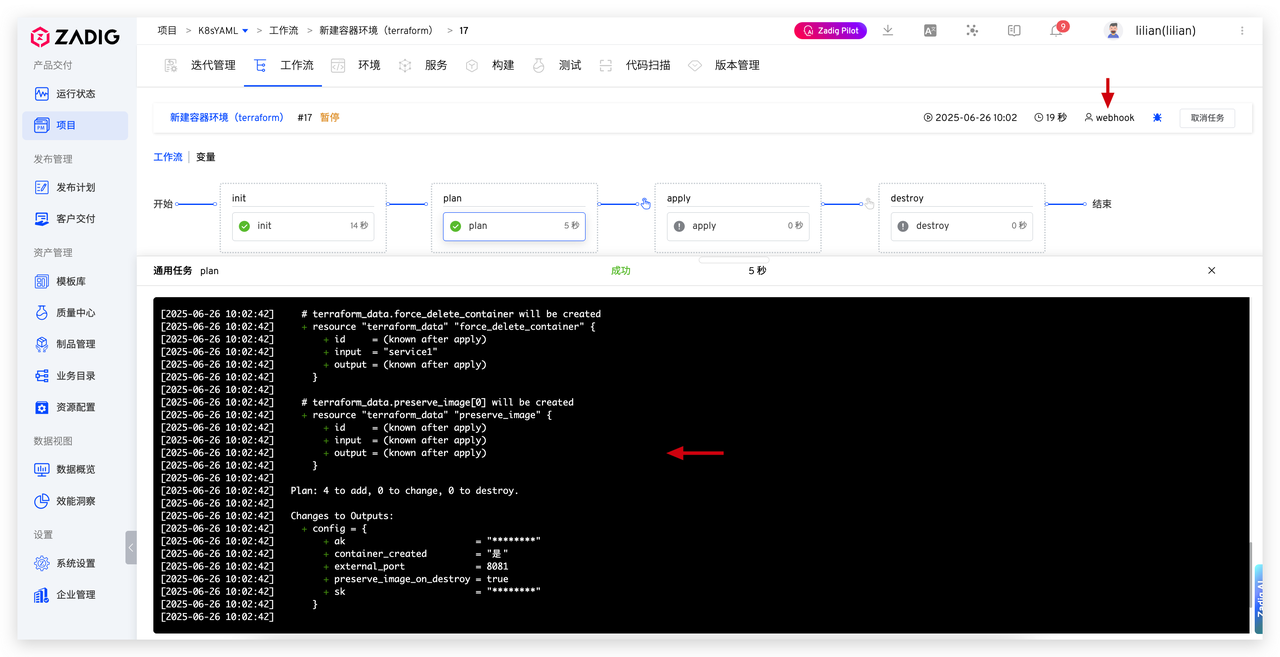
# GitOps Integration: Code as Change
By configuring "Git Triggers", Zadig can monitor code changes in Terraform repositories, implementing true GitOps processes:
- Terraform file changes automatically trigger workflows
- Automatically complete the full process of Init → Plan → Approval → Apply
- Every change is traceable, auditable, and rollback-able
# Summary of Results: From Manual Operations to Standardized Automation
With Zadig's enhanced capabilities for Terraform, enterprises have achieved best practices for automated infrastructure management:
- Every infrastructure change is driven by code and controlled by approval
- Sensitive information is encrypted throughout, eliminating leakage risks
- Shared storage across stages maintains state consistency, preventing environment drift
- Full process standardization and reproducibility improve change efficiency and reliability
This solution upgrades traditional manual operations to efficient, secure, and auditable DevOps pipelines, significantly enhancing enterprise infrastructure management capabilities in the cloud-native era.
# Conclusion
Through deep integration of Zadig with Terraform, enterprises have achieved full-process automated management of Infrastructure as Code (IaC), transforming traditional manual operations into standardized, auditable CI/CD pipelines. While ensuring security compliance (including sensitive information protection and manual approval), operational efficiency has significantly improved, with change velocity increased by 5 to 10 times. This solution effectively achieves the "fast, reliable, repeatable" goals pursued by DevOps, establishing industry best practices for IT operations in the cloud-native era.






